SoftwarePlaza IT Magazine
Login to your Account
Create Affiliate Account
Trouble Signing In?
Enter your email below to request a Reset Password Link
-
How to Achieve Real-Time Visibility with Upwind’s eBPF-Powered Platform
Achieve real-time cloud security with Upwind’s eBPF-powered platform. Learn how runtime visibility reduces noise, stops exploits, and protects AI and Kubernetes workloads.
-
9 Facts You Need to Know About SpiceDB’s Relationship-Based Access Control
Discover how SpiceDB uses ReBAC, low-latency architecture, and centralized authorization to deliver scalable, flexible, and AI-ready access control for modern apps.
-
How Beagle Security Helps Organizations Move Beyond Vulnerability Scanners
Discover why traditional scanners fall short and how Beagle Security enables continuous, API-focused testing for faster, stronger application security.
-
October 2025 Sees Sharp Rise in Supply-Chain Breaches and Ransomware Activity
Ransomware and supply-chain attacks surged in October 2025, exposing weaknesses in third-party systems and reshaping cybersecurity priorities for enterprises.
-
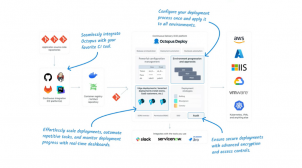
How Octopus Helps Implement Security and Operational Policies for Healthier Platform Adoption
Discover how Octopus Deploy automates security and operational policies to drive healthier, compliant, and developer-friendly platform adoption.
-
Latest Updates in Data Privacy and Governance Laws Around the World in 2025
Explore the latest 2025 data privacy and AI governance laws across regions and understand what future regulations mean for your business and digital strategy.
-
Red Hat OpenShift AI Flaw Puts Hybrid Cloud Systems at Risk of Full Takeover
A critical flaw in Red Hat OpenShift AI (CVE-2025-10725) lets low-privileged users gain full cluster control, putting hybrid cloud AI workloads at serious risk.
-
How IBM Instana uses Teleport to manage access to their cloud infrastructure
IBM Instana needed to secure access to its sensitive cloud infrastructure while boosting developer agility. Discover why they chose Teleport to replace VPNs and shared credentials, simplifying compliance audits (SOC 2, FedRAMP) and eliminating management overhead across their rapidly scaling, multi-cloud environment.
-
Unlimited access to Docker Hardened Images: Because security should be affordable, always
The cost of security shouldn't limit protection. Docker now offers unlimited access to its Hardened Images (DHI) catalog via an affordable subscription. Get near-zero CVEs, a 95% smaller attack surface, and SRLabs-validated security with SBOM/VEX support for every team, from ML workloads to FedRAMP-ready environments.
-
Expanding Docker Hardened Images: Secure Helm Charts for Deployments
Docker is simplifying Kubernetes security! Discover how new Helm charts in the Docker Hardened Images (DHI) Catalog give users a secure, compliance-ready alternative after the Broadcom/Bitnami changes. Deploy DHI by default, ensuring SLSA Level 3 security and SLA-backed patching for every Kubernetes workload.
-
Docker Hardened Images: crafted by humans, protected by AI
Docker’s Hardened Images (DHI) are secured by a dual approach: human expertise backed by AI. Discover how Docker’s internal AI guardrail spotted a critical logic flaw in an nginx-exporter update, blocked the release, and contributed the fix upstream, proving AI is the best force multiplier for security architects
-
Redefining Reliability: How Komodor is Building the Future of AI-Driven SRE
Discover how Komodor’s Claudia AI revolutionizes Kubernetes reliability through autonomous issue detection, investigation, and remediation powered by multi-agent AI systems.